Top 3 Featured Softwares
List of Top Vulnerability Management Software

PatrolServer

By PatrolServer
PatrolServer is a specialized software solution designed for security and patrol management. It provides a centralized platform to plan, execute, and monitor security patrols, ensu...
View Profile

Table of Content
What are Vulnerability Management Tools?
Vulnerablity management tools are special software platforms designed to identify, test, prioritize and remove safety weaknesses in the IT environment. These tools continuosly test networks, applications and systems for potential hazards or errors that can be exploited through malicious actors. A complete vulnerability management platform goes beyond primary scanning; it helps organizations proactively cope with vulnerabilities and decrease universal security risks.
1. Life Cycle of Vulnerability Management Tools
Comprehending the life cycle of vulnerability management software is essential for implementing an effective security strategy.
Asset Discovery and Vulnerability Assessment
The method begins by figuring out IT property and scanning for recognized vulnerabilities. This critical step helps lay the foundation for effective vulnerability management by establishing visibility throughout your infrastructure. Leading vulnerability management tools provide automated discovery and actual-time scanning capabilities to locate threats early. In the context of a vulnerability management software comparison, platforms with comprehensive asset mapping stand out for accuracy and depth.
Vulnerability Prioritization
Detected vulnerabilities are prioritized according to their risk level, exploitability, and effect on the business. Top vulnerability management tools utilize ML and threat intelligence to improve the prioritization procedure. Selecting the right vulnerability management software in USA enables your team to effectively address the most critical risks.
Remediation and Mitigation
This step involves making use of patches, converting configurations, or the usage of compensating controls to remove or lessen risk. Leading vulnerability management tools automate a lot of this method, assisting teams act quickly and exactly. Effective vulnerability management software supports seamless remediation workflows and minimizes downtime through crucial updates.
Validation and Monitoring
After remediation, the system verifies that the fix is effective and keeps monitoring the surroundings for any potential threats. Ongoing validation guarantees that vulnerabilities are not reintroduced through future updates or misconfigurations. Modern vulnerability management software in USA utilizes automated monitoring to maintain a secure posture.
Reporting and Improvement
Reports provide valuable insights into trends, compliance gaps, and overall performance metrics, which helps refine protection strategies. Effective vulnerability management tools make use of detailed reporting to assist selection-making and enhance compliance. Selecting the right vulnerability management platform enhances transparency and aids in long-term security planning. Integration with compliance management software helps track audit readiness and ensures that all regulatory gaps are identified and addressed efficiently.
2. Future Trends in Vulnerability Management Tools
The future of cybersecurity is growing rapidly, where vulnerability management tools paves the route through smart, automated and integrated solutions.
AI-driven Prioritization
Future vulnerability management tools will more and more leverage ML and AI to refine danger scoring, contextualize risk, and propose high-impact fixes. For example, platforms now use facts-driven exploit prediction models (such as EPSS) to rank vulnerabilities more appropriately—focusing mitigation on actual-global threats rather than simply raw CVSS scores. As a result, vulnerability management software becomes smarter, ensuring teams address critical issues first. This trend underscores why any vulnerability management software comparison should weigh AI‑powered risk prioritization heavily.
Automated Risk Assessment
Automated risk assessment tools are gaining prominence for their ability to offer real-time, records-driven risk scoring and automatic remediation workflows. Vendors like Qualys VMDR, AlertLogic, and Vanta now provide integrated solutions that automatically scan, assess compliance, and prioritize threats. These vulnerability management platforms reduce manual overhead, permitting security teams to proactively manage vulnerabilities without bottlenecks.
DevSecOps integration
The shift toward DevSecOps continues, integrating continuous security checks directly into development pipelines. Modern vulnerability management platforms embed dynamic and static testing, code analysis, and automated remediation into CI/CD workflows. Academic studies highlight how AI‑driven security tools enhance DevSecOps by reducing manual effort and accelerating feedback loops. This integration ensures that security is a constant, automated part of the vulnerability management lifecycle.
Quantum-Resistant Protocols
With the looming future of quantum computing, organizations are adopting post-quantum cryptography (PQC) and quantum-resistant measures. Governments and enterprises are preparing for quantum threats by implementing new cryptographic standards like CRYSTALS‑Kyber and Kyber‑based key exchanges (e.g., PQXDH), alongside hybrid classical–quantum methods. NIST has already standardized three PQC algorithms, with more in development. In vulnerability management tools, this trend means embedding crypto-agility—supporting rapid switchover to quantum-safe algorithms as needed.
Zero Trust Architecture
Zero Trust is increasingly woven into vulnerability management tools to reduce implicit trust and micro-segment networks. Over 72% of organizations are pursuing zero-trust architectures, combining continuous identity verification with strict access policies across every network zone. Future vulnerability management platforms will integrate scan data with zero-trust controls, enabling granular enforcement, policy automation, and adaptive risk responses.
Automated Scans and Remediation
Full automation—continuous, scheduled scanning coupled with automatic patch deployment—will be core to future vulnerability management platforms. These systems, enhanced with AIOps and self-healing capabilities, will detect threats, trigger remediation, verify fixes, and adjust scans dynamically. The end result: vulnerability management tools that reduce human latency and ensure tighter closure of security gaps.
3. Benefits of Vulnerability Management Tools
Implementing robust Vulnerability Management Solutions gives great advantages to businesses aiming to secure their virtual infrastructure.
1. Reduced Risk of Exploitation
By figuring out vulnerabilities earlier than they can be exploited, these tools reduce the chance of a breach. They help mitigate risks proactively. These Vulnerability Management Tools play a critical function in lowering an corporation’s exposure to threats. A robust vulnerability management solution complements cybersecurity by addressing issues earlier than attackers can make the most of them. When paired with a risk management SaaS solution, vulnerability management tools can offer centralized visibility into organizational threats and streamline risk scoring.
2. Smaller Attack Surface
Regular scans and patches assist decrease open ports, outdated software, and other vulnerabilities, effectively shrinking the attack surface. These vulnerability management tools reduce potential assault vectors in both hybrid and cloud environments. By continuously enhancing endpoint security using the best endpoint protection software in conjunction with vulnerability scans, these tools make it extra tough for attackers to make the most out of systems. A sturdy vulnerability management solution ensures that an business’s IT landscape stays resilient in opposition to ever-evolving threats.
3. Protection of Sensitive Data
Vulnerability management solutions play an important role in securing sensitive data, including financial figures, customer information and ownership resources. They identify gaps in data handling systems and offer comprehensive visibility into sensitive assets. These platforms ensure that data protection measures are consistently applied. A robust vulnerability management software in USA should also support regulatory compliance and proactively mitigate data-related risks.
4. Faster Response Times
Automated alerts and integrated remediation features enable IT teams to respond swiftly, preventing vulnerabilities from escalating. These vulnerability management platforms streamline response workflows by providing contextual insights. With actual-time updates and analytics, modern vulnerability management software complements operational efficiency and decreases the time required to resolve incidents.
5. Improved Resource Allocation
Organizations can increase productivity by focusing their IT and security resources on strategic goals, contrary to just responding to incidents. Vulnerability management tools assist allocate both human and technological sources correctly. The best vulnerability management software enables teams to concentrate on innovation while continuously optimizing security protocols.
4. Key Components of Vulnerability Management Tools
Grasping the fundamental components of modern vulnerability management tools is crucial for choosing a solution that aligns with your organization's requirements.
1. Asset Discovery
This feature allows the tool to identify and catalog all devices and applications within a network. Gaining visibility into the IT surroundings is the first step in handling vulnerabilities. Modern vulnerability management tools provide automated asset discovery for both on-premise and cloud environments. These abilties are critical for an effective vulnerability management solution.
2. Vulnerability Scanning
Vulnerability scanners check devices and structures for diagnosed vulnerabilities, misconfigurations and compliance troubles. Vulnerability scanners often operate hand-in-hand with network security software to perceive unauthorized access points and network misconfigurations.This procedure usually makes use of industry-standard databases including CVE. The notable vulnerability management tools encompass non-stop scanning capabilities, allowing them to locate rising threats in real-time. These capabilities are crucial to recollect whilst making vulnerability management software comparision with a purpose to select the simplest solution.
3. Vulnerability Assessment
Assessment involves analyzing scan outcomes to determine the severity and potential impact of every vulnerability. Risk scores help guide remediation efforts. Leading vulnerability management tools utilize contextual risk analysis to prioritize threats based on the value of assets and their exploitability. This approach improves the accuracy of remediation plans, making vulnerability management solutions more effective.
4. Patch Management
This component automates the application of software updates and patches. Timely patching is important to retaining secured surroundings. Vulnerability management tools streamline patch deployment procedure, making sure steady protection throughout endpoints. The best vulnerability management software includes intelligent patch scheduling to minimize downtime and business disruption.
5. Vulnerability Remediation
Remediation tools provide targeted actions to address identified issues. Some solutions even integrate with ticketing systems to automate workflows. Leading vulnerability management tools facilitate automated remediation actions, allowing teams to respond more efficiently. These features improve the overall effectiveness of vulnerability management solutions and help close security gaps more quickly.
6. Cloud Vulnerability Management
Modern platforms, often integrated with loud security software, evaluate vulnerabilities in cloud infrastructures, including containers, virtual machines (VMs), and APIs, to provide comprehensive protection. These vulnerability management tools, specifically designed for cloud environments, help secure the dynamic and scalable systems used by contemporary enterprises. For businesses in the USA that are doing vulnerability management software comparison, cloud readiness is an important criterion to consider.
5. Best Vulnerability Management Tools in USA
Selecting the best vulnerability management software in USA involves understanding your organization’s specific needs and security posture. Choosing the best software for computer security starts with identifying tools that can proactively detect and fix vulnerabilities across all environments.Below, we review the top five platforms that provide a combination of advanced features, scalability, and user-friendliness to help you make an informed decision.
1. ManageEngine Vulnerability Manager Plus
ManageEngine Vulnerability Plus is a vulnerability software that helps businesses in managing vulnerabilities and ensuring compliance. Basically, it identifies, checks, priortizes, and remediates security weaknesses across endpoints and networks.
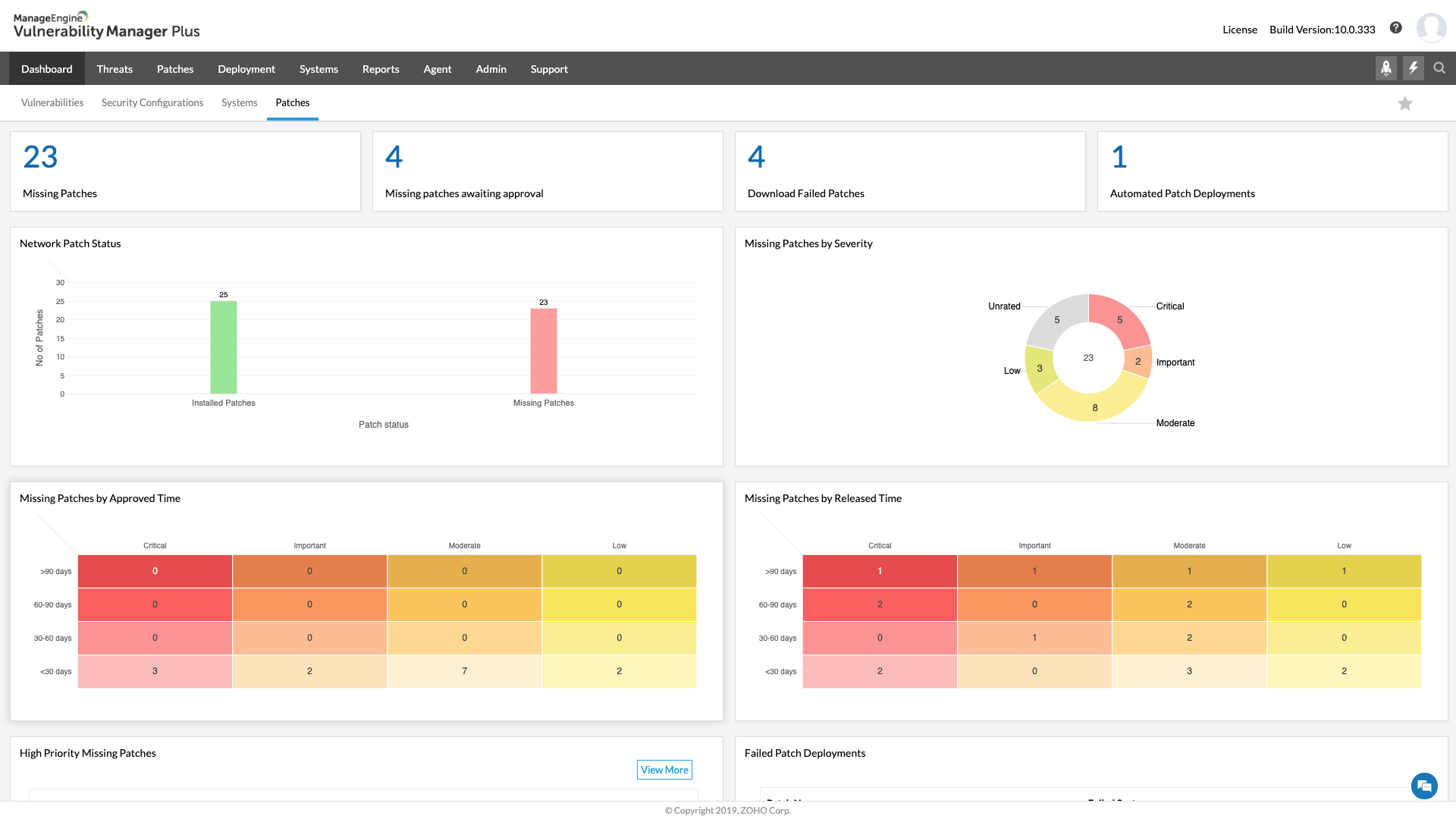
Features
-
Automated Patching
-
CIS Compliance Management
-
Identity and Access Management
-
IT operations management and observability
-
Advanced IT analytics
Pros
-
User-friendly Interface
-
Comprehensive Features
Cons
-
Patching Limitations
-
Web application scan scheduling challenges
Pricing: Offers free plan. Professional plan costs $695 annually and Enterprise plan costs $1195 annually.
2. Surfshark
Surfshark is basically known for robust VPN services but on the flip side it also functions as vulnerability management software. Surfshark offers Data Vulnerability Thermometer that tests how much is the risk if your data is breached.
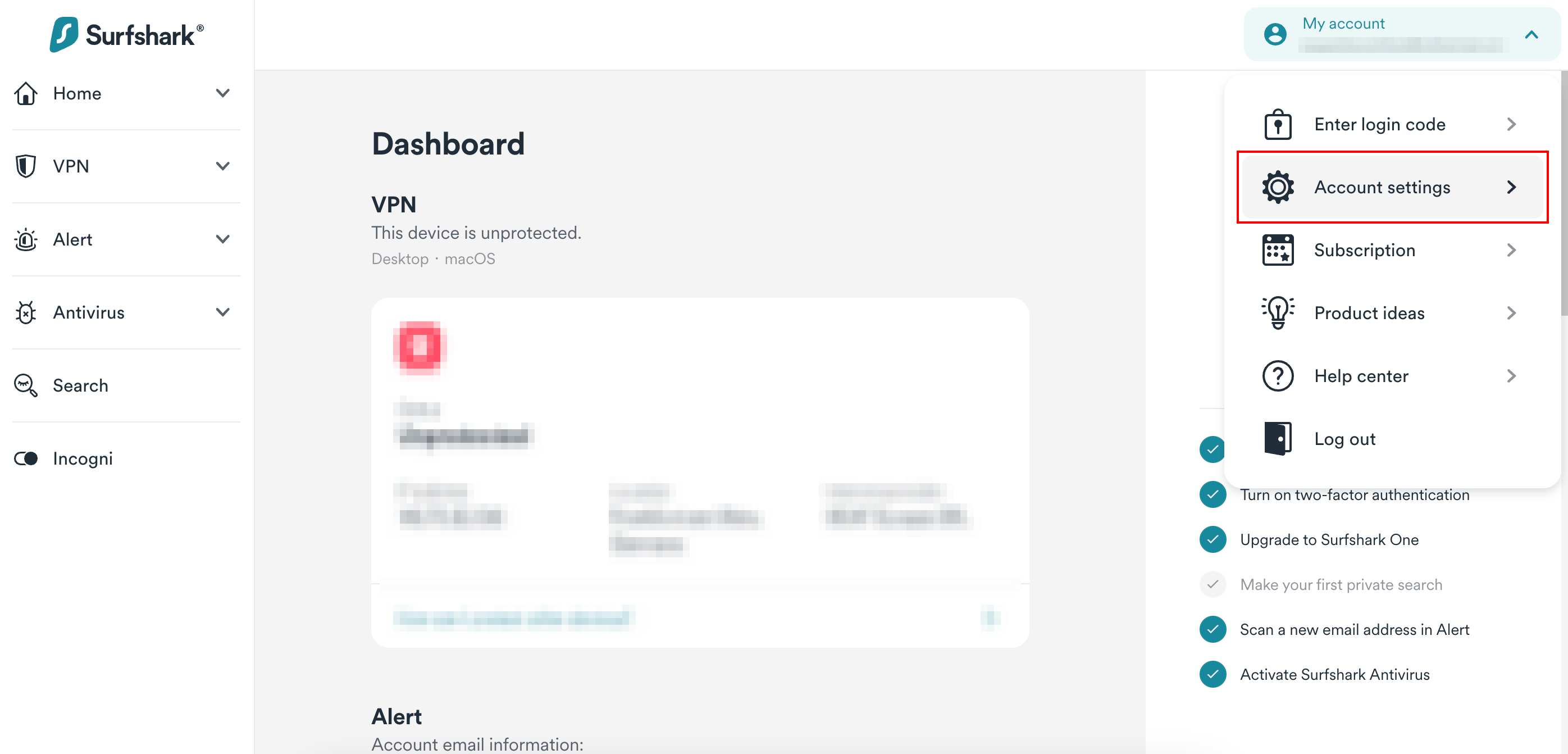
Features
-
Data Vulnerability Thermometer
-
Surfshark Alert
-
Data breach monitoring
-
Malware Attack monitoring
-
Surfshark KillSwitch
Pros
-
User-friendly Interface
-
No-logs policy
Cons
-
Potential for Speed Drops
-
Some Servers may be overloaded
Pricing: Surfshark plans are divided into three time durations: 1 month, 12 months, and 24 months. Surfshark Starter is $15.45 for 1 month, $3.19 for twelve months, and $1.99 for twenty-four months. Surfshark One is $17.95 for 1 month, $3.39 for twelve months, and $2.49 for twenty-four months. Surfshark One is $20.65 for 1 month, $6.09 for 12 months, and $3.99 for twenty-four months.
3. Qualys VM
Qualys VM is a vulnerability management software that offers cloud-based capabilities for cybersecurity and helps organizations to track, assess, and remediate vulnerabilities across networks, systems, and applications. It specializes in finding vulnerabilities before they exploit the data.
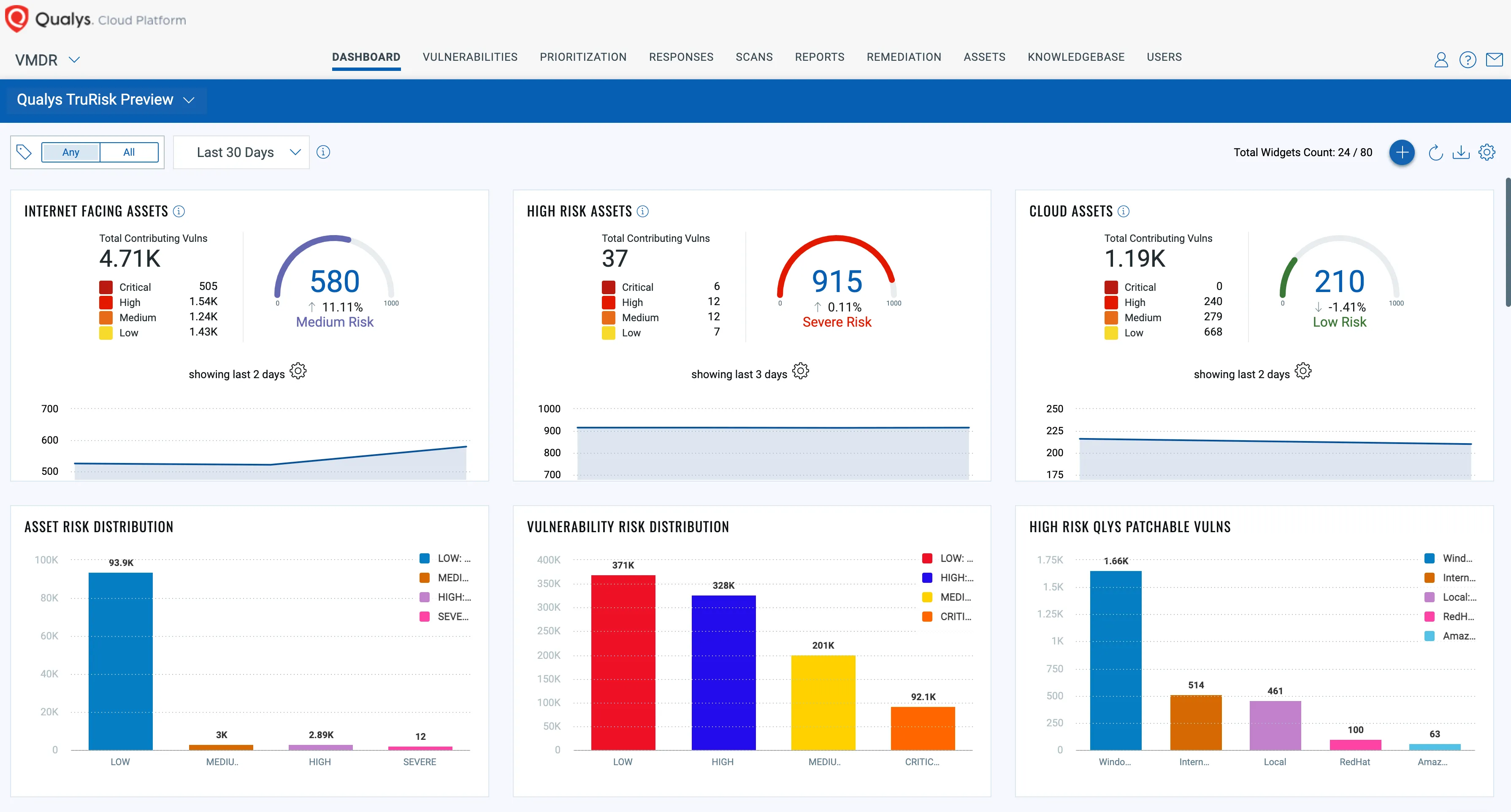
Features
-
Asset Management
-
Risk Remediation
-
Cloud Security
-
Vulnerability & Configuration Management
-
Threat Detection & Response
Pros
-
Comprehensive Threat Visibility
-
Flexibiliity and Scalability
Cons
-
Slow Customer Support
-
Limited In-Depth Reporting
Pricing: Take a Free Trial for pricing
4. Tenable.io
Tenable.io is a vulnerability management software that provides full network visibility to organizations predicting potential attacks and respond quickly as possible. The software’s accurate vulnerability coverage assists in decreasing false positives and negatives, ensuring the security teams fully understand security risks in web applications.

Features
-
Cloud Exposure
-
Vulnerability Exposure
-
OT/IoT Exposure
-
Identity Exposure
-
Exposure Analytics
Pros
-
Comprehensive Vulnerability Management
-
Customizable Dashboards and Reports
Cons
-
Scan Limitations
-
Complex setup
Pricing: Tenable offers annual pricing based on number of Assets. For initial 100 assets, Tenable offers 3 subscriptions: 1 year ($5,782), 2 years ($11,274.90), and 3 years ($16,478.70).
5. InsightVM
InsightVM is an advanced vulnerability management software that offers expert threat intelligence assisting organizations to reduce risk meaningfully. The software allows organizations to have continuous visibility into security risks spread across the network.
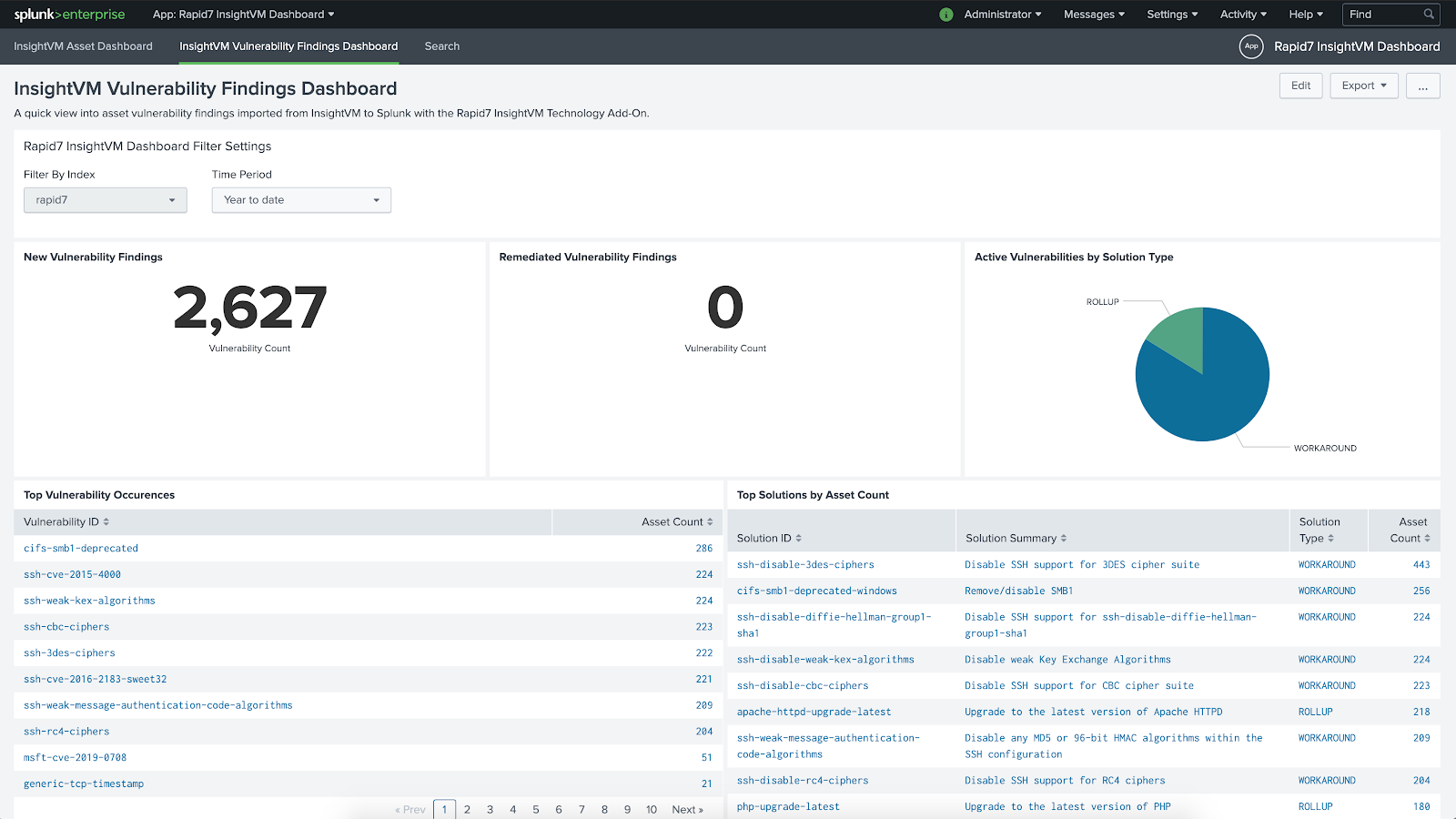
Features
-
Exposure Management
-
Attack Surface Management
-
Vulnerability Management
-
Threat Intelligence
-
Cloud-Native Application Protection
Pros
-
User-friendly Interface
-
Comprehensive Vulnerability Management
Cons
-
Complex setup process
-
Expensive for small businesses
Pricing: Offers free trial. InsightVM pricing is based on number of assets. 250 Assets costs $26.25/year. 500 Assets costs $23.18/year. 750 Assets costs $21.43/year. 1000 Assets costs $20.54/year. 1250 Assets costs $19.43/year.
6. Who Uses Vulnerability Management Tools?
Vulnerability Management Tools are used across industries, including:
-
Financial institutions to comply with regulatory mandates and secure customer data
-
Healthcare providers for HIPAA compliance
-
Government agencies to protect critical infrastructure
-
Tech companies to secure agile development pipelines
-
Retailers to guard customer transactions and POS systems
Whether it’s a small startup or a Fortune 500 organization, each company with a virtual footprint can gain from a reliable vulnerability management solution. Many organizations pair vulnerability management tools with the best cybersecurity software to create a layered defense strategy.
7. Conclusion
It is important to choose proper vulnerability management tools to preserve a strong cybersecurity position. Whether you run a small company or a large organization, the best vulnerability management software will help you cope, prioritize and meet the first dangers before it escalates to critical situations. With functions like actual-time tracking and cloud compatibility, modern tools are more effective than ever. With functions like actual-time tracking and cloud compatibility, modern tools are more effective than ever. Know your needs, check distinctive software options, and ultimately make a selection to buy the one that scales along with your commercial enterprise.
8. Why Do Companies Need a Vulnerability Management Tool?
In a time of developing cyber threats, corporations can not manage to be reactive. They need proactive solutions that constantly monitor their digital assets. Vulnerability Management Tools enable organizations to:
-
Uncover unknown and emerging vulnerabilities
-
Ensure compliance with enterprise policies like HIPAA, GDPR, and PCI-DSS
-
Minimize the time and cost involved in incident response
-
Build a scalable security infrastructure
Without an effective vulnerability management solution, businesses are exposed to information breaches, ransomware attacks, and reputational damage.
 Researched and Written by
Researched and Written by 


