Scalable identity verification has become such an absolute must for modern businesses that it has become impossible to go on without them. They provide security, regulatory compliance, and customer trust - all things you can't miss out on. The identity verification market reflects this as well, and here are some numbers to prove that - it's projected to reach $18.12 billion by 2027.
Nobody wants to be the victim of fraud and online fraud losses exceeded $41 billion in 2022, which means there's an urgent need to take steps. On top of that, 85% of organizations consider scalability a critical factor when selecting identity verification providers to accommodate growing verification volumes efficiently.
The scalability of solutions allows businesses to adapt to expanding operations, ensure consistent compliance across global markets, and enhance customer onboarding experiences - basically everything a business wants to do. As digital ecosystems become more complex, adopting scalable and automated identity verification processes is no longer a choice but a necessity for maintaining operational integrity and fostering long-term growth
Exploring Scalable Identity Verification Methods For Modern Businesses
Okay, so we've covered that you need identity verification and you need it to be scalable - no objections there. But how do you make the choice? What is the right type of identity verification for you? Below you'll find our top choices which are not, by any stretch of the imagination, the end of the line.
From biometric technologies to document verification, businesses require solutions that not only ensure security but also adapt to varying customer volumes without compromising speed or accuracy - or to put it simply that they are scalable. To make the most of these solutions, it's essential to have the right identity management software in place.
Biometric Identification: Scalability Through Advanced Technologies
Biometric identification is something we have all become familiar with by now - facial recognition, fingerprints, iris scans, and voice recognition— you probably use one of these methods to unlock your phone. Once again, the numbers reflect the interest 2027, the biometric identification market is expected to reach $68.6 billion by 2027. How do biometric achieve
scalability - right now through built in solutions and in the future with integration with AI-driven systems, which can handle large volumes of data quickly and accurately.
Businesses will use cloud-based solutions that allow for on-demand scaling, enabling the system to process growing numbers of verification requests. On top of that we can expect numerous advances in technology to further boost the use and widespread nature of these verification systems.
iDenfy’s identity verification solution enables biometric authentication and ID document verification in under 3 minutes with up to 99 % accuracy. The platform supports more than 3,000 document types from over 200+ countries and combines facial recognition with 3D liveness detection tools and manual review team efforts for maximum precision and compliance.
Document Verification: Leveraging Automation For Scale
Document verification has been and continues to be a staple of identity verification - and with good reason. While it is a legacy model of identity verification it has very much use in our current online world. It relies on the authentication of government-issued IDs, passports, and driving licenses. Scalability is here achieved through automation tools that scan and analyze documents in real time - whereas the current practice now is that this needs to be done by a human.Additionally, a CPIC criminal record check can be integrated into this process to provide a more comprehensive background assessment.
So, in the future we can expect automated document verification platforms to handle verification requests quickly. To further enhance scalability, businesses will probably opt for API-based integrations that connect verification processes with their digital platforms, ensuring seamless and efficient operations as demand increases.
Knowledge-Based Authentication (KBA): Enhancing Flexibility For Growth
KBA methods rely on personal information only the right person would be able to know. This mainly includes historical data or security questions, to verify an individual's identity. In the online world this verification method is considered somewhat traditional by now and has faced criticism for vulnerability to data breaches. A more modern approach will incorporate dynamic questioning and real-time data analysis for improved security and scalability - making them less hackable.
To ensure scalability, businesses can implement AI-driven KBA systems that automatically adapt to growing customer bases. These systems pull from a broad range of data sources, allowing for the quick formulation of personalized verification questions. Moreover, integrating KBA systems with cloud infrastructures enables businesses to accommodate fluctuating verification volumes efficiently. Regular updates and algorithm enhancements ensure that KBA systems remain effective against evolving fraud tactics, maintaining their reliability as a scalable verification option.
Two-Factor Authentication (2FA): Building Scalable Security Layers
2FA strengthens security by requiring users to provide two distinct forms of identification—such as a password and a verification code sent via SMS or email. This method is scalable due to its adaptability across various platforms and ease of integration with existing systems.
Scalable 2FA systems rely on automated code generation and secure delivery protocols to ensure efficiency, even when processing large volumes of authentication requests. Cloud-based 2FA solutions offer businesses the flexibility to adjust capacity based on demand. Advancements in mobile technology we've already mentioned, such as biometric-enabled devices, allow businesses to integrate multi-factor authentication, ensuring security without compromising user experience. As cyber threats evolve, adaptive 2FA solutions can also incorporate behavioral analytics to detect anomalies, adding another layer of scalable security.
Blockchain-Based Identity Verification: Decentralization For Growth
Now here's something novel, blockchain technology offers a decentralized approach to identity verification, ensuring data integrity and scalability. The jist of it is that tamper-proof records that can be verified independently eliminate the need for centralized data storage, reducing the risk of breaches.
Scalable blockchain verification systems will use smart contracts to automate and streamline verification processes. These systems can manage vast amounts of verification data, supporting businesses as they expand across global markets. On top of that, further refined blockchain solutions will be inherently flexible, allowing for easy integration with other verification methods like biometrics or document authentication - stuff we've already covered.
Adaptive Risk-Based Authentication: A Dynamic Approach to Scalability

We have already said several times that digital threats evolve only to become more sophisticated so how do you tackle that as a business? The textbook answer is that businesses will require identity verification methods that not only scale efficiently but also adapt dynamically to risk levels - and this is the important part. This is where adaptive risk-based authentication (RBA) comes into play.
Unlike static identity verification methods, RBA evaluates real-time risk factors before determining the level of authentication required. This approach ensures that verification processes remain both secure and frictionless, enhancing user experience while maintaining robust security.
How Adaptive RBA Works
Rather than applying a one-size-fits-all approach to identity verification, RBA adjusts verification requirements based on context. It assesses multiple risk signals, such as:
-
Geolocation discrepancies – If a user logs in from an unusual country, additional verification steps (such as biometric authentication or an OTP) may be triggered since that's the most usual risk.
-
Device and browser fingerprints – Changes in a user’s usual device or browser settings can indicate potential fraud attempts, though this sometimes can be a little too much.
-
Behavioral analytics – If a user’s typing speed, mouse movements, or navigation patterns differ significantly from their norm, the system may prompt additional authentication.
-
Login frequency and velocity – Multiple login attempts from different locations in a short time frame can trigger a higher security threshold.
By continuously analyzing these factors, adaptive authentication ensures that lower-risk interactions require minimal verification, streamlining customer experience while heightening security for suspicious activities.
Scaling RBA for Growing Business Needs
One of the primary advantages of adaptive authentication is its scalability. Instead of applying blanket security policies across an entire user base, RBA dynamically allocates security resources where they are most needed. This flexibility allows the following things:
-
Reduce friction for legitimate users (we've all seen almost paranoid login notifications), improving onboarding and retention.
-
Optimize verification costs by minimizing unnecessary authentication steps.
-
Strengthen fraud detection by continuously evolving in response to emerging threats.
-
Support global operations by tailoring security measures to different risk environments.
Many enterprises are integrating risk-based authentication with other identity verification technologies, such as biometrics, document verification, and 2FA, (all of which we've already covered above) to create a multi-layered security approach. This combination ensures a seamless but highly secure experience for customers while maintaining compliance with evolving regulations.
Future Trends in Adaptive Authentication
The future of RBA lies in real-time risk intelligence and context-aware authentication. Businesses will increasingly leverage:
-
Dynamic risk engines that analyze vast datasets to refine verification strategies.
-
Privacy-enhancing technologies (PETs) to balance security with user data protection.
-
Decentralized identity models, where users control their credentials without central databases storing sensitive data.
Wrapping Up
In the ever evolving landscape of digital security, businesses must also consider the ethical implications of identity verification. Usually ethics in new tech advancements come as an afterthought which can cause problems down the road. However, it will be key to ensure that processes respect user privacy and promote transparency. As identity verification grows in volume so will this need as well. Investing in adaptive verification technologies that prioritize user consent and data minimization will be essential for long-term trust. As innovation continues, businesses that prioritize both security and ethical standards will be better positioned to navigate regulatory changes and enhance their market credibility. And one final point - it will be necessary to find the thin line to walk on between being safe and not being boring to your customers.
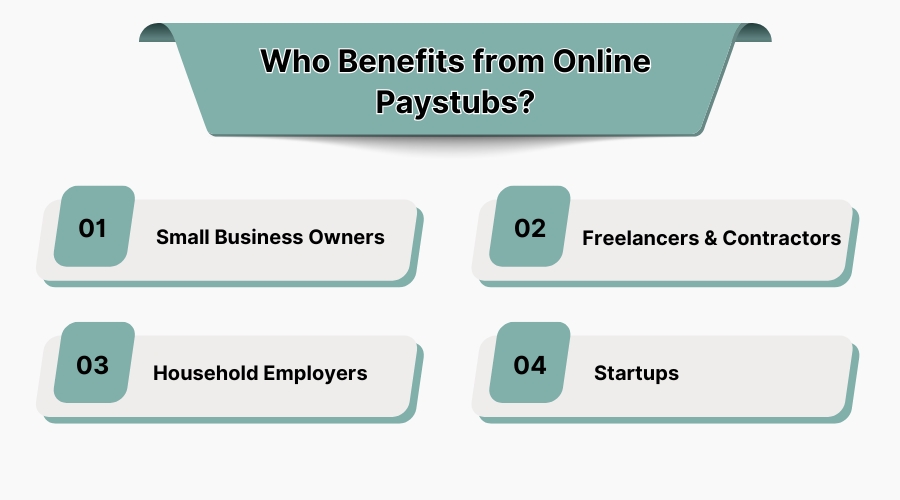
Scalable identity verification ensures security, regulatory compliance, and customer trust while allowing businesses to efficiently handle growing verification volumes.
They integrate advanced technologies like biometrics, adaptive authentication, and blockchain to minimize fraud risks and protect sensitive data.
Finance, healthcare, e-commerce, and government sectors see the most benefit due to high security and compliance demands.
Yes, many solutions are designed to comply with regulations like the CCPA, ensuring secure and compliant identity management.