Outsourced development changes security and compliance not by introducing exotic threats, but by quietly shifting how control, responsibility, and risk are distributed inside a business. For US-based founders and executives, this shift directly influences SOC 2 readiness, HIPAA exposure, enterprise sales cycles, and ultimately company valuation.
According to IBM’s Cost of a Data Breach Report 2024, 48% of reported data breaches involve third parties, and organizations working with external vendors take more than 60 additional days on average to detect and contain incidents. Those delays rarely result from advanced attacks. Much more often, they stem from unclear ownership, fragmented visibility, and assumptions that no longer hold once development responsibility is shared.
When software is built by multiple organizations at the same time, security stops being a task owned by one internal team. Compliance stops living in static policy documents. Both become properties of coordination, operational discipline, and repeatable engineering processes.
This shift is subtle. Many founders only notice it during due diligence, during an audit, or after a customer asks a question that is harder to answer than expected.
A practical operational comparison of engagement models is outlined in What Is Offshoring vs Outsourcing?. When reviewed specifically through a security and compliance lens, the difference between these models is not theoretical. It directly affects how predictable risk becomes as the business scales.
Why does outsourcing reshape security architecture before coding starts?
Outsourcing reshapes security before the first feature reaches production because it changes who the system must trust.
To deliver real value, external developers need real access. Not sanitized demo credentials, but working permissions to source repositories, CI/CD pipelines, cloud infrastructure, secrets managers, and environments that behave like production. From a delivery perspective, this is unavoidable. From a risk perspective, it multiplies identities, credentials, and configuration paths that must remain aligned over time.
The Ponemon Institute reports that 56% of organizations have experienced security incidents tied to third-party access, while only 34% maintain continuous visibility into vendor permissions. This gap explains why many incidents go unnoticed until their impact becomes visible.
Most failures do not begin with malicious behavior. They begin with convenience.
A token issued during onboarding that never expires.
A role granted broadly “to avoid blocking work.”
A CI pipeline duplicated for speed and never reviewed again.
Each shortcut feels rational in isolation. Together, they erode control.
For entrepreneurs, the key insight is simple: outsourcing does not weaken security by default. It weakens security when governance is implicit instead of designed.
Security architecture becomes a coordination problem rather than a tooling problem
Founders often assume security issues can be solved by adding tools. Another scanner. Another dashboard. Another policy document.
In outsourced environments, tools matter far less than alignment.
Once multiple teams contribute to the same system, security outcomes depend on whether they follow the same rules. Are code reviews mandatory or optional? Are CI checks enforced or advisory? Who owns the decision when something looks suspicious?
Gartner research indicates that organizations with fragmented development workflows are 35% more likely to face recurring security findings related to third-party access. These findings rarely reflect missing controls. They reflect inconsistent execution.
Well-governed environments feel boring. Access behaves predictably. Pipelines behave consistently. Logs follow familiar patterns. Evidence already exists when auditors ask for it.
Poorly aligned environments feel chaotic, even when no breach occurs.
For a founder, predictability matters more than theoretical perfection.
Compliance becomes a workflow issue rather than a documentation exercise
With outsourced development, compliance stops living in policy binders and starts living in day-to-day execution.
SOC 2, HIPAA, and ISO 27001 still define control objectives. What changes is where evidence is generated. Code reviews. Access approvals. Deployment logs. Incident tickets. These artifacts now span organizations, tools, and time zones.
This explains why many compliance failures feel frustrating rather than dramatic. Nothing appears obviously broken. Yet when auditors ask how access is revoked or how incidents are escalated, answers arrive in fragments.
The NIST Cybersecurity Framework explicitly treats third-party access as part of an organization’s own risk surface
For business leaders, this framing matters. Vendors are not “outside the perimeter” once they interact with production systems.
Compliance friction increases when:
-
ownership is unclear
-
evidence is scattered across tools
-
standards are interpreted differently by each team
It decreases when workflows are unified.
Repeating risk patterns appear across most outsourced development setups
Despite differences in industry or company size, the same operational risks appear repeatedly.
Common risks and practical mitigation strategies
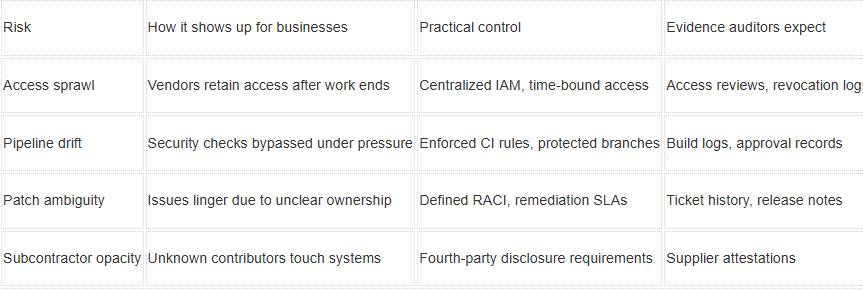
The important takeaway is this: these risks usually signal missing structure, not weak engineering talent.
Organizations that address them deliberately tend to reduce repeat audit findings within a few quarters.
Delivery models influence how risk is experienced, not whether it exists
Nearshore, offshore, and hybrid models can all be secure. None are inherently risky.
What changes is how friction appears.
Nearshored teams often benefit from overlapping work hours, enabling faster reviews and real-time clarification. Offshore teams can scale effectively, but they typically require stricter documentation, clearer escalation paths, and more formal handoffs to avoid misunderstandings.
For founders, geography is rarely the deciding factor. Operational clarity is.
Organizations with stable outcomes usually share three traits:
-
Unified development workflows
-
Centralized identity and access management
-
Clearly defined incident-response paths that include vendors
When external teams are treated as part of the delivery system rather than transactional suppliers, security incidents become manageable events rather than existential threats.
Mature organizations reduce outsourcing risk by eliminating exceptions
Companies that handle outsourcing well tend to do one thing consistently. They eliminate special cases.
Security expectations are embedded into onboarding, tooling, and delivery metrics instead of enforced after something goes wrong. Identity management is centralized. Pipelines are shared. Monitoring is continuous.
Gartner notes that organizations with unified vendor-governance programs are 35% less likely to receive material audit findings related to third-party development. One analyst summarized it plainly: visibility solves more problems than control.
A US-based SaaS company preparing for enterprise sales reported smoother SOC 2 audits after consolidating all development activity into a single security dashboard. No radical changes were introduced. Questions became easier to answer because evidence already existed.
Predictability is the goal.
Vendor selection and onboarding define long-term security posture
For many companies, the highest-risk moment in outsourcing is onboarding.
Early decisions establish long-term patterns. Access models. Documentation habits. Communication norms.
Mature organizations formalize onboarding by:
-
granting access incrementally rather than upfront
-
documenting security responsibilities explicitly
-
enforcing CI/CD standards from day one
These practices reduce future friction and simplify compliance as the business scales.
What founders should evaluate before outsourcing development?
Entrepreneurs evaluating outsourcing partners often focus on cost and speed. Security requires different questions.
Practical evaluation points include:
-
how access is granted, reviewed, and revoked
-
who owns vulnerability remediation
-
how incidents are reported and escalated
-
whether subcontractors are disclosed
Clear, specific answers usually indicate operational maturity. Vague answers often predict future compliance friction.
Responsible outsourcing strengthens trust and long-term company value
In modern software businesses, well-governed outsourcing signals maturity. Enterprise customers, investors, and regulators expect leaders to understand how systems are built and how risks are managed.
Outsourcing will always influence security and compliance because it reshapes development itself. The outcome depends on how deliberately governance is designed.
When outsourcing is treated purely as a cost lever, security fragments. When it is treated as an extension of engineering operations, trust compounds.
Strong governance does not slow growth. It protects it.
Risk grows only when access and responsibility are blurry. If vendors use the same logins, pipelines, and rules as the internal team, outsourcing rarely becomes the weak point. The real problem starts when access is given once and never revisited.
Yes, if controls are simple and visible. Auditors look for repeatable processes, not employment contracts. One shared toolset and one owner per control usually solve most audit questions.
Not really. The difficulty comes from slow clarification, not from distance. Clear written rules and fixed escalation paths usually matter more than time zones.
SOC 2 is what customers ask for. NIST helps structure internal decisions. ISO 27001 becomes relevant when enterprise or global clients appear. Most companies don’t need all three at once.
Assuming the contract will handle security. Contracts don’t revoke access, review code, or respond to incidents. Day-to-day workflows do.